Running your code in containers is a great way manage and deploy software. All of the code needed to run your app is inside one or more containers. You can move these containers from environment to enviornment by creating images and running these images in each environment (as containers).
If you’re using Docker, or a similar alternative, you already know all of this. That’s great but how are you managing security within each container?
Do you know what’s in your container?
You worked hard to get your application to run well in a container. You took care to write good code and follow best practices. You tested and deployed. Now you’re done, right? Not exactly.
Every container contains numerous linux packages that your custom code needs to run. Are all of these secure? Is your base linux distro secure? How do you know there aren’t some known threats below your custom code?
What is image scanning?
I brought up images at the beginning for a reason. These same images that can bundle some or all of your software can be scanned (inspected) for known vulnerabilities. Even if you know all of the packes are golden at launch, there’s a chance some vulnerability creeps in as you iterate on your software over the next few weeks or months. Just because it was green lit last month doesn’t mean some hacker won’t penetrate it next month.
Since all of your containers are based on an image, why not let a tool check what is baked into your image and see if there are any known vulnerabilities?
Since DevOps is about automation it makes sense let a security tool help you keep your application safe. It doesn’t replace your due diligence, it just helps you keep tabs of all those components that make up your container…while you sleep even.
Anchore
At Arroyo Labs we’ve been using Anchore since it was in Beta. I’ll show you the benefits of container scanning by using the Anchore tool as an example.
You can start by checking any container images that your software needs to run. You can search for your base image easily in the UI.
Here is an example of searching for erdiko. We have a bunch of erdiko images I published on Dockerhub and Anchore scans them all. Every time I push a new image to Dockerhub Anchore gets notified and runs a new scan.
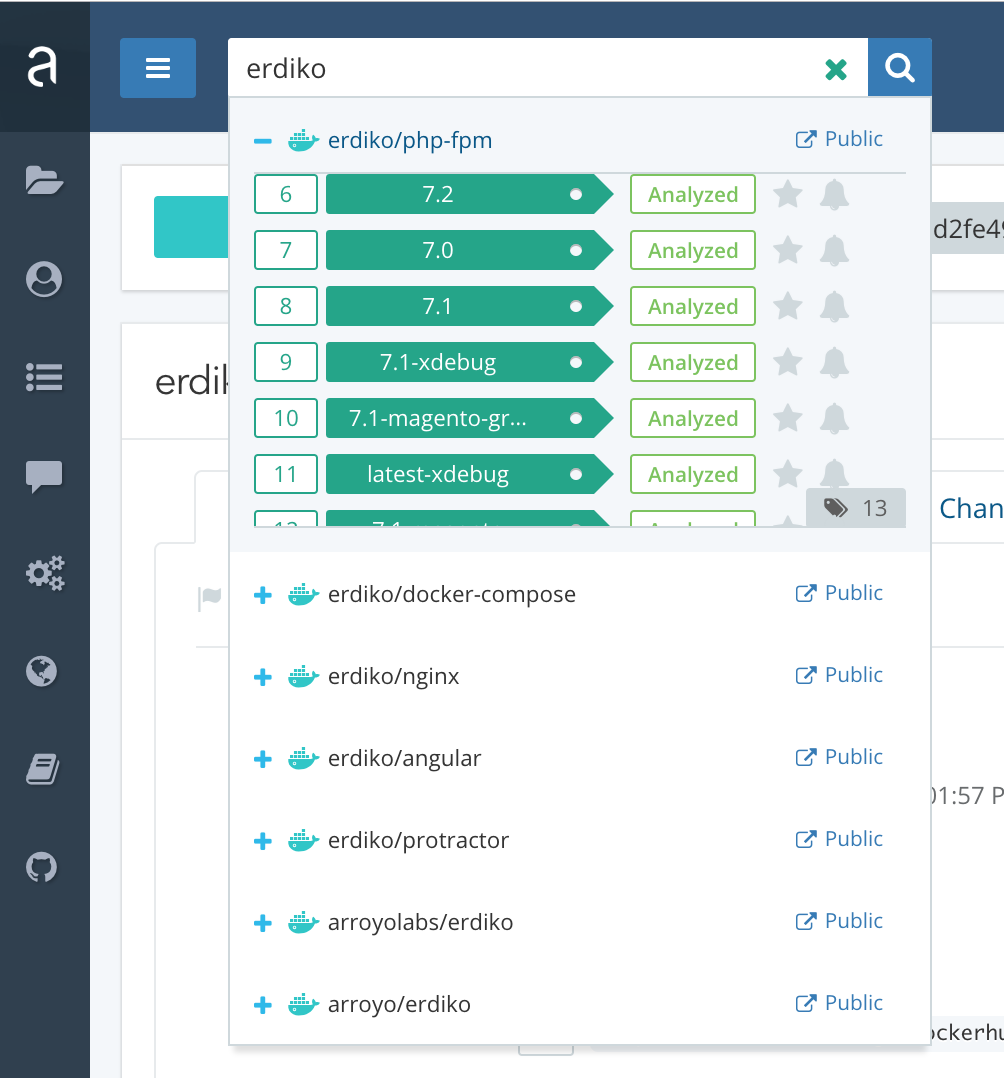
Everytime I push an update to an image on github, dockerhub creates a new build. Soon after Anchore will rescan the image built and the results will be available for anyone to see. Since the image is open source Anchore scans it for free and anyone can see the results.
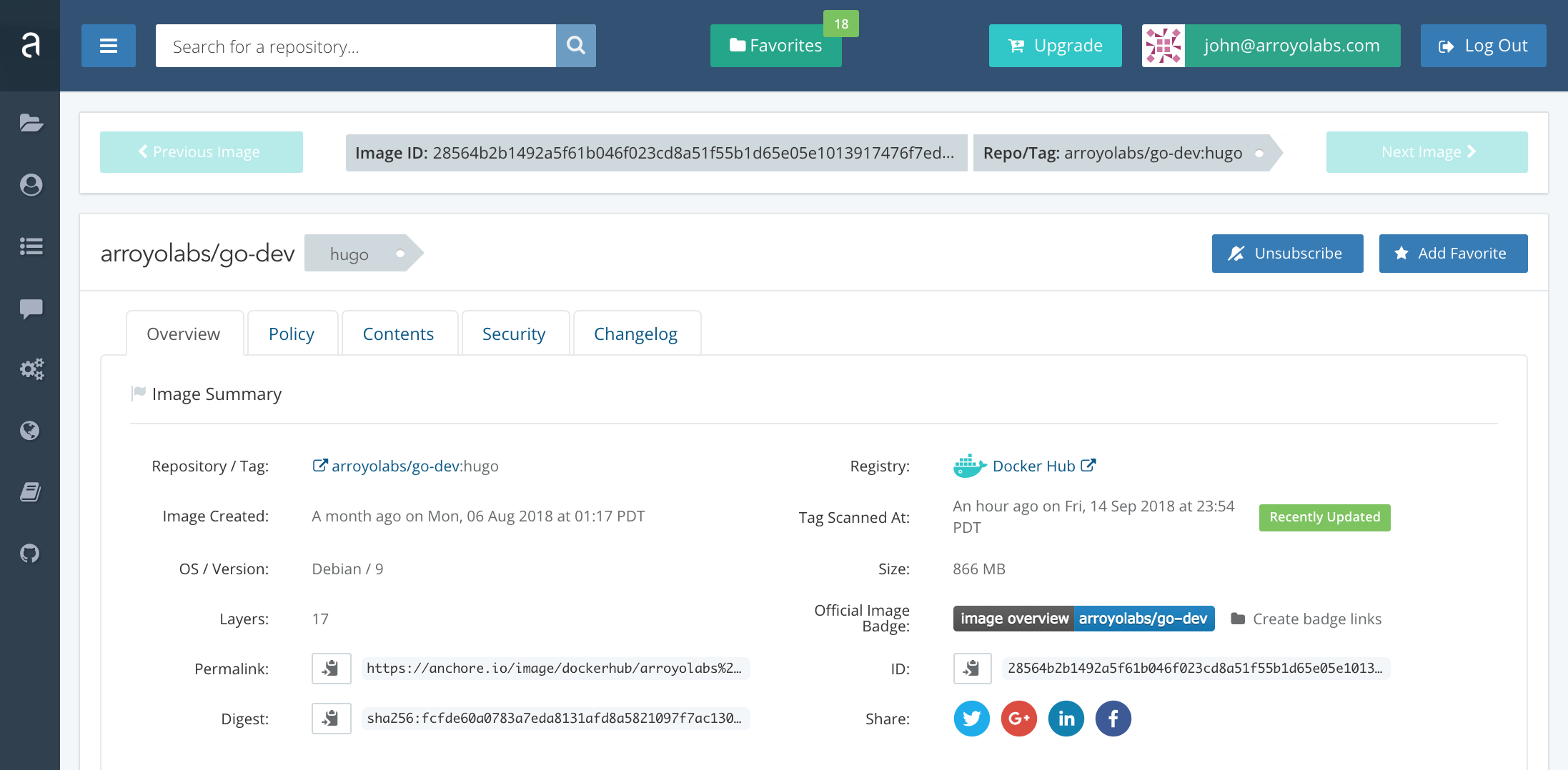
Now back to your base image. Once you find your base image, click on the tag and you can explore its security, changelog, policy, etc.
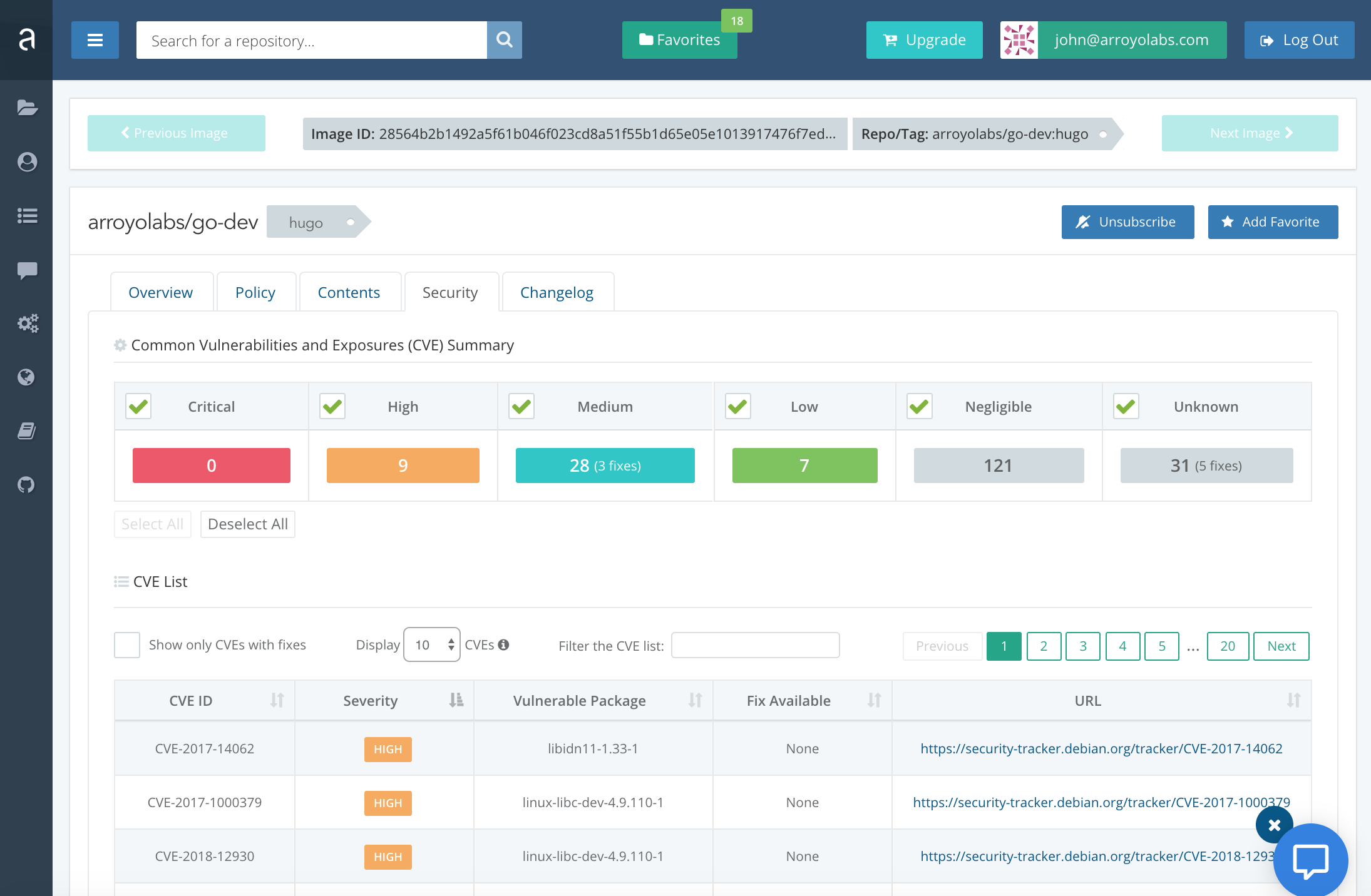
I see a few high in this particular image. Some of these are irrelevant to the use case of the container but some of these I should address with an update.
You can filter by threat level and research the vulnerability to see if the threat is real or not for your software. See the image below.
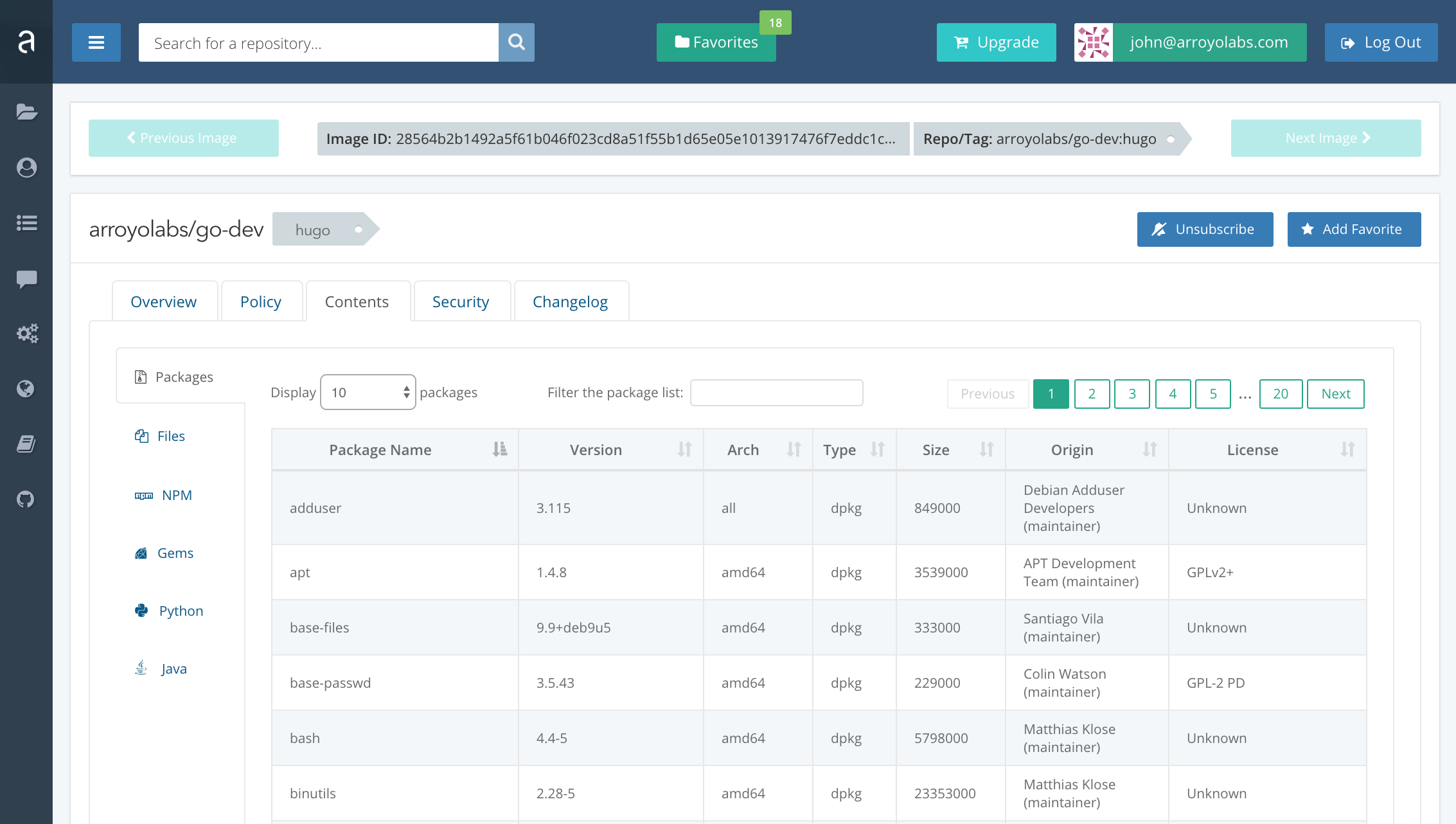
You can also drill down into all the different packages that make up your linux container. You can go as deep as you want into this image.
What about CI/CD?
All of the good Docker security tools out there have APIs so you can integrate with your continuous integration system. Some have plugins for quick and easy integration with their partners. Out of the box integration with Jenkins and Kubernetes is common. While others work easily with Open Shift or CircleCI. As long as there is an API available you can make scanning work with any CI system. You might just need to add some elbow greese.
If you have open source images published on Dockerhub it is very easy (and free) to set up anchore scanning.
One of the more ideal scenarios is to publish your release as an image. You tag it and bag it and move it through your workflow. Somewhere along that automation why not send your image to be scanned and based off of the results you fail the build or let it continue. To start maybe you only fail if a critical comes up…or maybe you fail if a medium shows up.
Other popular vendors
There are numerous tools out there. These are ones that I either liked from Dockercon or have demoed elsewhere. Like other areas of cloud and container tools there aren’t obvious winners or killer features that break the mold. In some cases the differences are minor. It comes down to what works best in your environment and what features fit your security needs. One many deal with scanning volume better but another have more flexible settings for a diverse team, some may have additional security features or better pricing. No one size fits all here…but who knows we’ll probably see consolidation here over the next few years like we’ve seen in other areas of devops and security.
